CUSTOMERS WHO TRUST US
CUSTOMERS WHO TRUST US
How it works?
SPOG operationalizes cyber governance by validating controls, collecting evidence, orchestrating remediation, and quantifying risk continuously.
Risk observability Simplified
Get expert advice tailed to your needs
Who is it for
Built for teams responsible for security governance, service operations, and infrastructure resilience.
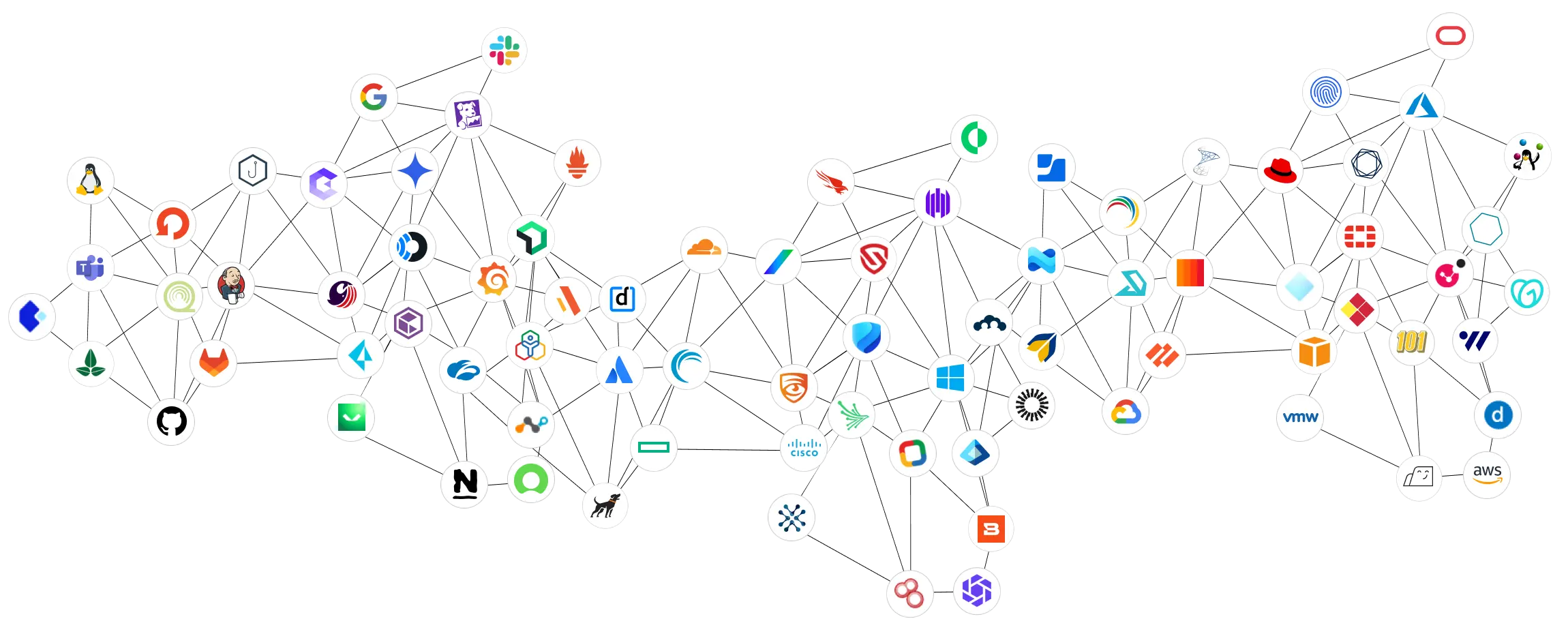
140+ pre built integrations
Bring data from every corner of your IT ecosystem into one control view
Technology
VENDORS
Endpoint Security (10)
Alert Management (9)
Device Management (6)
Patch Management (6)
Firewall (4)
Cloud (6)
Domain Registrar (5)
DNS (5)
Monitoring System (7)
SASE (Private Access)
140+ pre built integrations
Bring data from every corner of your IT ecosystem into one control view
Browse All Integration 
Arista
Network Switch

Rukus
Wireless Network
servicenow
Service Desk
Redhat
Patch Management
Darwinbox
HRMS

Manageengine
CMDB

Newrelic
Monitoring System

Zscaler
Web Proxy

Veeam
Backup

Synk
CSPM

Elastic
Logging

Github
Sourcecode Repository
jenkins
Pipeline
Guardicore
Micro Segmentation

knowbe4
Security Awareness

Windows
Operating System

Dell
Hardware

Akamai
Email Security
Slack
Chat

Cortex XDR
Alert Management

SentinelOne
Endpoint Security
Palto Alto
Alert Management

Scalefusion
Device Management

Godaddy
Domain Registrar
ManagEngine
Device Management

okta
Identity Provider
Redhat
Patch Management

Google Cloud
Cloud

fortinet
Firewall

Tucows
Domain Registrar
Frequently Asked Questions
Quick answers on how our platform unifies compliance, risk, and IT operations.
Didn’t find your answer?
Talk to us